Prüfpunkte
Create the VM with desired configurations
/ 20
Download vulnerable web application files on the VM
/ 20
Enable the Web Security Scanner API
/ 20
Run a Web Security Scanner scan and detect application vulnerabilities
/ 20
Correct vulnerabilities and rescan your application using Web Security Scanner
/ 20
Identify Application Vulnerabilities with Security Command Center
Overview
Introduction
In this lab, you will use Web Security Scanner—one of Security Command Center's built-in services—to scan a Python Flask application for vulnerabilities. Web Security Scanner identifies security vulnerabilities in your App Engine, Google Kubernetes Engine (GKE), and Compute Engine web applications.
This service crawls your application, following all links within the scope of your starting URLs, and attempts to exercise as many user inputs and event handlers as possible. It can automatically scan and detect four common vulnerabilities, including cross-site-scripting (XSS), flash injection, mixed content (HTTP in HTTPS), and outdated/insecure libraries.
Web Security Scanner enables early identification of vulnerabilities and delivers very low false positive rates. You can easily set up, run, schedule, and manage security scans.
Scenario

Cymbal Bank is an American retail bank with over 2,000 branches in all 50 states. It offers comprehensive debit and credit services that are built on top of a robust payments platform. Cymbal Bank is a digitally transforming legacy financial services institution.
Cymbal Bank was founded in 1920 under the name Troxler. Cymbal Group acquired the company in 1975 after it had been investing heavily in Cymbal Group's proprietary ATMs. As the bank grew into a national leader, they put strategic emphasis on modernizing the customer experience both in-person at their branches and digitally through an app they released in 2014. Cymbal Bank employs 42,000 people nationwide and, in 2019, reported $24 billion in revenue.
Cymbal Bank is interested in developing a new banking application for their corporate clients using Google Cloud technology. Application security is critical, and the CTO wants to see how Google Cloud can identify and mitigate application security vulnerabilities. As a Cloud Security Engineer, you are tasked with demonstrating Security Command Center's cutting-edge application vulnerability scanning features.
Objectives
In this lab, you will perform the following tasks:
- Launch a vulnerable Python Flask application on a Compute Engine instance
- Use Web Security Scanner to scan the application and find vulnerabilities
- Fix the application vulnerability
- Scan the application again and verify vulnerabilities no longer exist
Setup and requirements
For each lab, you get a new Google Cloud project and set of resources for a fixed time at no cost.
-
Sign in to Qwiklabs using an incognito window.
-
Note the lab's access time (for example,
1:15:00), and make sure you can finish within that time.
There is no pause feature. You can restart if needed, but you have to start at the beginning. -
When ready, click Start lab.
-
Note your lab credentials (Username and Password). You will use them to sign in to the Google Cloud Console.
-
Click Open Google Console.
-
Click Use another account and copy/paste credentials for this lab into the prompts.
If you use other credentials, you'll receive errors or incur charges. -
Accept the terms and skip the recovery resource page.
Task 1. Launch a Virtual machine and deploy a vulnerable application
In this task, you will set up the infrastructure to demonstrate an application vulnerability to Cymbal Bank's CTO. More specifically, you will deploy a virtual machine, obtain the application code and introduce a vulnerability that will be detected by Web Security Scanner. This application is a simple form that receives a user's input and outputs it without any changes.
-
On the Google Cloud Console title bar, click Activate Cloud Shell (
). If prompted, click Continue.
-
Create a static IP address that will be used for scanning a vulnerable web application:
- Run the following command to output the static IP address you just generated:
-
Copy the IP address (a single line of the output) and save it in a notepad.
-
Run the following command to create a VM instance to run the vulnerable application:
The startup script will install python-flask, a Web Application Framework, which is used for running a simple Python application demonstrating cross-site scripting (XSS) vulnerability, which is a common web application security vulnerability.
- Open a firewall rule for Web Security Scanner to access a vulnerable application. Note the source ranges from which Web Security Scanner scans applications.
Click Check my progress to verify the objective.
-
Open the navigation menu and select Compute Engine > VM Instances.
-
Then click on the SSH button next to your instance:
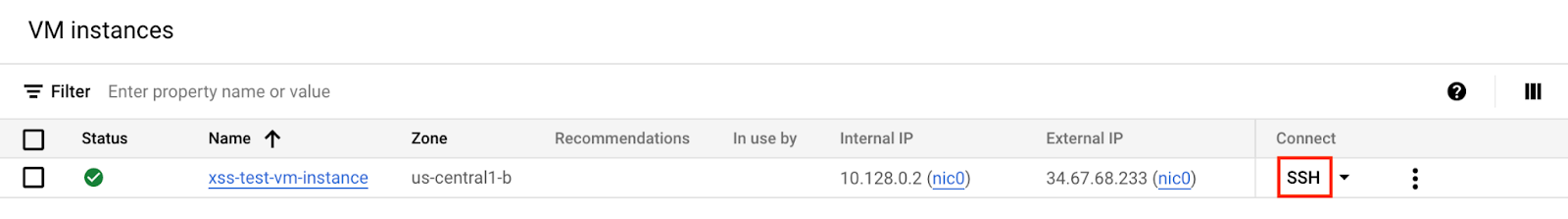
This will open an SSH connection to your VM instance in a new window.
- In this SSH window (Not in Cloud Shell), run the following command to download and extract the vulnerable web application files:
- Now run the following command to deploy your application:
- Soon after, you should receive a message that indicates your application is up and running:
-
Find the static IP address of the VM you copied into your notepad earlier.
-
Replace
YOUR_EXTERNAL_IPin the URL field below with that IP address, and open the URL in a new browser tab:
-
A Cymbal Bank corporate banking portal with a web form should appear.
-
In the web form enter the following string:
- Now press the POST button.
You should see the following alert window:
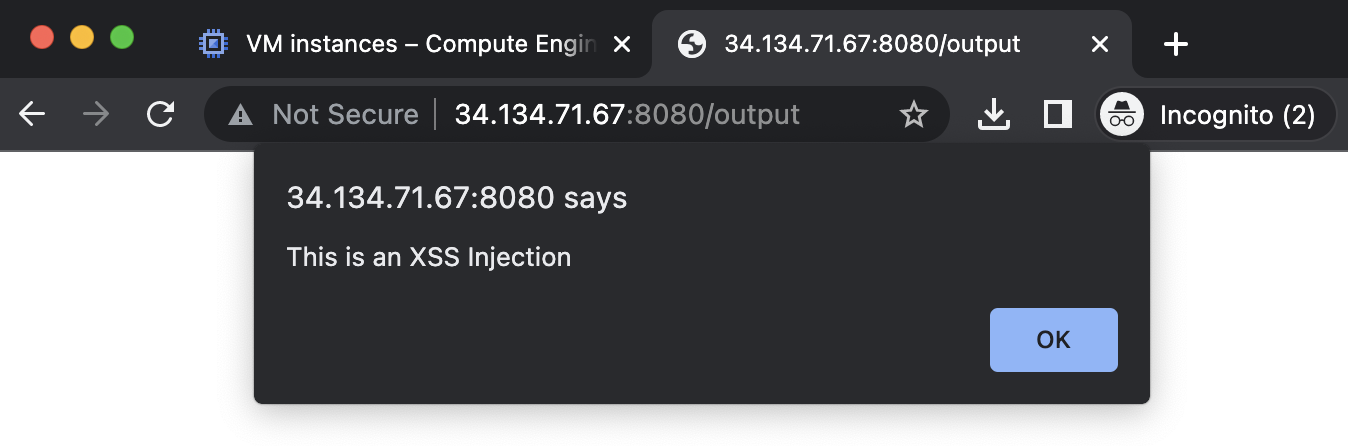
This is a common vulnerability in web applications: a cross-site scripting vulnerability. Cross-site scripting (XSS) is a vulnerability that enables attackers to run malicious scripts in users' browsers in the context of your application. Your browser interprets a string as a legitimate Javascript and executes it.
An attacker who uses an XSS bug to inject JavaScript into an HTML page gains virtually unlimited access to the logged-in sessions of the victims who visit the page: they may steal user data, tamper with it, change privacy or security settings, or even completely alter the way the product looks and operates. Even more, an XSS vulnerability in one application, no matter how inconsequential, may jeopardize other content within the same domain.
This is one of many application vulnerabilities that Web Security Scanner can help you identify.
Click Check my progress to verify the objective.
Task 2. Scan the application with Web Security Scanner
Now that we've launched our vulnerable application, it's time to demonstrate Web Security Scanner's abilities to the CTO. In this task, you will configure and set up a scan of the application to find security vulnerabilities.
-
Switch back to the browser tab displaying the Cloud console.
-
Open the Navigation menu and select APIs & Services > Library.
-
In Search for APIs and services type Web Security Scanner.
-
Click Enable API to enable the Web Security Scanner API.
Click Check my progress to verify the objective.
-
Open the Navigation menu and select Security > Web Security Scanner.
-
Click + New Scan.
-
The Starting URLs field should be pre populated with your static IP address.
-
Add the port number 8080, so that the Starting URL looks like the following:
- Take a minute to review the remaining fields on the Create a new scan screen:
- Authentication: a property that can be used to provide application credentials to allow the scanner to authenticate to an app while scanning.
- Schedule: a property that can be used to schedule scans to run automatically.
- Export to Security Command Center: a property that allows you to automatically export scan configurations and scan results to Cloud Security Command Center after scans are finished.
-
Verify the Authentication is still set to None and that Schedule is set to Never.
-
Click Show More to investigate the remaining settings.
-
Click Save to create the scan.
- Click Run to start the scan
- Return to your SSH session in your separate window.
If the session timed out, run the following command to restart your application:
In your SSH Window, you will begin to see logs generated similar to the example below—this is Web Security Scanner testing all possible URLs for potential vulnerabilities:
You may see log statements with the following HTTP status codes:
- 200: A successful request, where the HTTP server answered with an OK response.
- 302: Indicates a resource is temporarily located elsewhere according to the Location header.
- 404: indicates that one or more resources were not found.
Check out this documentation for more information on HTTP status and error codes.
While the scan is running, feel free to explore the Results, URLs Crawled, and Details tabs. You can also check out this getting started video, or this vulnerability scanning video to learn more about Web Security Scanner.
- When the scan is done running, the Results tab should indicate the cross-site vulnerabilities.
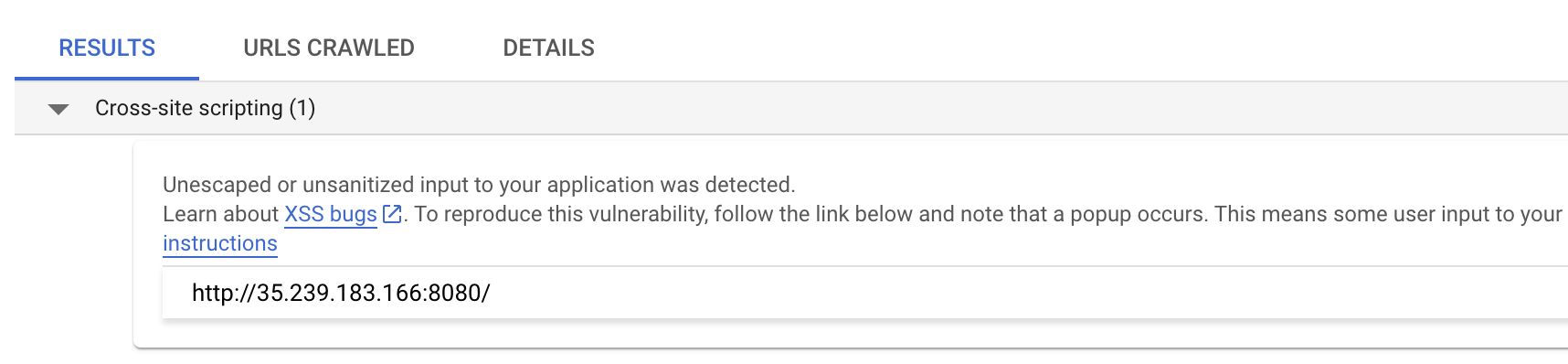
The Web Security Scanner was able to scan all starting URLs and detect the XSS vulnerabilities in Cymbal Bank's application. The ability to automate the detection of these critical vulnerabilities is a major benefit for security-minded organizations like Cymbal Bank. You will now fix the vulnerability in Cymbal Bank's application code and test once again.
Click Check my progress to verify the objective.
Task 3. Correct the vulnerability and scan again
Now that you have demonstrated Web Security Scanner can detect a XSS vulnerability, you will remediate the vulnerability and run the application scan again.
- Return to your SSH window that's connected to your VM instance.
- Stop the running application by pressing CTRL + C.
- Edit the app.py file using the nano editor by running the following command:
- locate the two lines that set the output string:
- Remove the ‘#' symbol from the first line and add it to the beginning of the next line (ensure that you indent your code properly!)
Your final lines must look like the following:
html_escape_table is a dictionary that contains one-to-one pairings of special HTML characters like "<" to their text representation. We use this table to escape special HTML characters so our form ingests and interprets submissions as raw text only. You can find more information here.-
Now type CTRL+X > Y > Enter to save your changes.
-
Now re-run the application:
-
Return to the Google Cloud Console (you should still have the Web Security Scanner page open):
-
Click Run at the top of the page.
In your SSH Window, you will start to see logs where Web Security Scanner tests application URLs for potential vulnerabilities:
-
While you are waiting for the results of the scan, login to the URL
http://<EXTERNAL_IP>:8080using your browser in a separate tab. -
You should see the web form once again.
-
In the web form enter the same string that you entered in before:
-
Now press the POST button.
-
Verify that this time you see the string displayed in the browser:
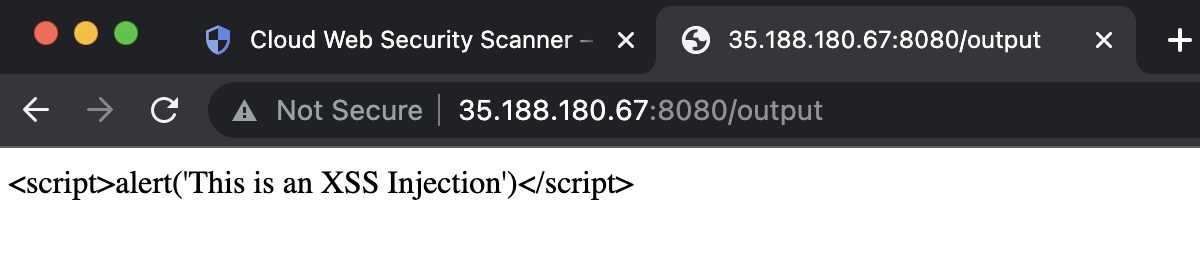
-
Return to the Google Cloud Console, where you left off on the Web Security Scanner page.
-
Click Run at the top of the page to re-scan your application.
-
Soon after, you will see that the results yield no more XSS vulnerabilities:
Well done! You have successfully demonstrated to the Cymbal Bank CTO how to identify and remediate XSS vulnerabilities with Google Cloud's powerful Web Security Scanner solution.
Click Check my progress to verify the objective.
Congratulations!
In this lab, you performed the following tasks:
- Launched a vulnerable Python Flask application
- Used Web Security Scanner to scan the application and find vulnerabilities
- Fixed the application vulnerability
- Scanned the application again and verified vulnerabilities no longer exist
End your lab
When you have completed your lab, click End Lab. Google Cloud Skills Boost removes the resources you’ve used and cleans the account for you.
You will be given an opportunity to rate the lab experience. Select the applicable number of stars, type a comment, and then click Submit.
The number of stars indicates the following:
- 1 star = Very dissatisfied
- 2 stars = Dissatisfied
- 3 stars = Neutral
- 4 stars = Satisfied
- 5 stars = Very satisfied
You can close the dialog box if you don't want to provide feedback.
For feedback, suggestions, or corrections, please use the Support tab.
Copyright 2022 Google LLC All rights reserved. Google and the Google logo are trademarks of Google LLC. All other company and product names may be trademarks of the respective companies with which they are associated.